Is your WordPress web site vulnerable to the attack?
The WordPress REST API was recently added and enabled by default on WordPress 4.7.0.If you are using WordPress versions: 4.7.0 or 4.7.1 you should immediately update to version 4.7.2 where WordPress patched the "then-secret zero-day vulnerability" security flaw.
What's this all about?
One of these WordPress REST API endpoints allows access (via the API) to view, edit, delete and create posts.Within this particular endpoint, a subtle bug allows visitors to edit any post on the site.
That could lead to the creation of two new vulnerabilities "Remote privilege escalation" and "Content injection bugs".
For the technical details of the injection, you can check Sucuri's post here.
Patchman in action!
If you are a Kualo shared or reseller hosting customer, then our automatic vulnerability patching system has already fixed the issue for you - even before Sucuri announced it: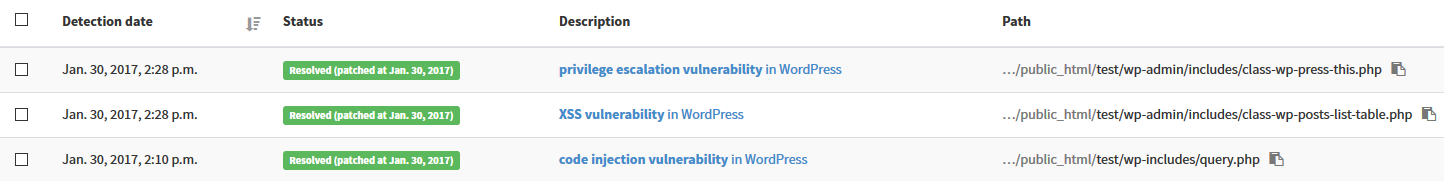
How great is that?
If you're a Kualo virtual or dedicated server customer and would like to add Patchman to your server, please get in touch!
Not with Kualo? Why not have us transfer your WordPress website to our hosting. We'll take care of the complete migration, and you can sleep easy knowing we have some of the best security of any web host.
Should you need any further information or assistance, please do not hesitate to contact us.